From data breaches to system slowdowns to denial-of-service disruptions, cyber attacks are a serious threat to firms of all sizes. Cyber security is crucial for survival, but many small businesses struggle to adopt the latest safety methods. By releasing its most effective security steps, Microsoft has provided smaller companies with the counsel they need to stay safe. To protect privacy and fend off pernicious programs, Microsoft practices:
Intuitive Identification
Microsoft carefully distinguishes employees with security clearance, sealing off sensitive data from anyone who cannot pass a multi-factor authentication program. This ensures that company secrets never fall into the hands of someone who is untrustworthy or lacks the expertise to properly handle it.
Although small businesses may not have the resources for sophisticated authentication, they can still control access to sensitive data. Create complex passwords for all private information, and distribute them only to trustworthy employees who understand the risks. Change the passwords regularly so that if an employee does leak data, the damage will be limited. The more you limit information access, the fewer avenues there are for a breach.
Consistent Classification
To bolster the effectiveness of its identification system, Microsoft catalogs all of its digital data and functions. It categorizes each piece of information according to how sensitive it is and then develops security measures in line with each category. As a result, the company keeps the most sensitive data as secure as possible without slowing down access to routine information.
Classification is a simple matter for small businesses. Financial access, systems controls, and private customer and employee data should receive the greatest protection. Less sensitive items should still be kept secure, but you can use simpler authentication methods. In general, the more damaging it would be for a piece of data to be released, the harder it should be to access it.
Surveying The System
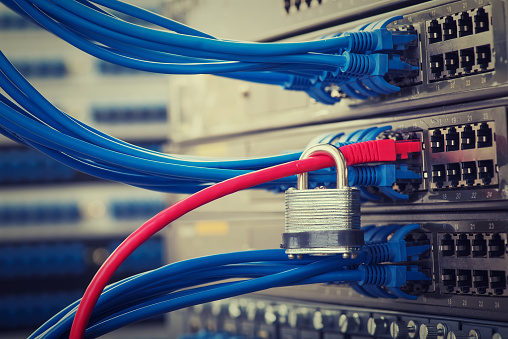
Microsoft monitors its computer systems extensively. Not only does it keep an eye on all activity on its networks, but it also keeps the hardware in secure locations with constant video surveillance. This ensures that no one will be able to physically damage computer equipment or upload malware through it.
Small companies don’t have the resources to monitor their hardware on this scale, but they can still install cameras in areas with valuable equipment. Combined with locking their doors at night, this lets them control access to sensitive company devices. They can also keep backup files in a locked room and limit access to the key.
Software Savvy
Hackers routinely devise new methods of attack, making previously effective security measures obsolete. To stay one step ahead, Microsoft updates its anti-malware programs regularly, sparing no expense to maximize defenses. Small businesses may not be able to afford the same caliber of software, but they also do not have to defend systems as complex as Microsoft’s. By following trends in software development and consulting a cyber security expert, they can determine the defenses they need and quickly put them in place.
Attack Analysis
Microsoft doesn’t wait for attacks to happen. It maps out the likely avenues of attacks, identifying vulnerabilities and acting quickly to shore them up. Small businesses should be just as proactive. A good way to start is by eliminating unnecessary or redundant functions; this simplifies the system, making it harder for an attack to catch your company off guard.
Nachman Networks provides cybersecurity insight and assistance to all Washington DC, Northern Virginia & Maryland firms. For more information, contact us at sales@nachnet.com or (703) 600-3301 today.